; Date: Tue Jul 10 2018
Tags: Face Recognition »»»» Big Brother »»»» Machine Learning »»»» China »»»»
Modern technology is gifting society with many wonders, including democratization by giving more creative power to individuals. In some countries the Internet is not allowed to be used for democratization, but for authoritarian control. One particular area is facial recognition technology which is how social media networks like Facebook can automatically tag your pictures with your friends. That same technology can be aimed at a crowd, and used to implement real-time tracking of where folks walk throughout a city. Supposedly the benefit is catching wrong-doers, but in every movie about ubiquitous monitoring the government doesn't use the information for the benefit of all, but to squash freedom.
As an example, let's look at
a news report by the NY Times. This report focuses on Megvii, a Chinese company with well developed facial recognition technology. Its services are being used by the Chinese government for a wide range of purposes. Where in the USA this sort of technology gives us the heeby-jeebies, and therefore the USA Government is not openly using facial recognition technology, China is a different story with a government that has strong authoratarian tendencies from the start.
We should recall that in June, employees of Amazon and Google both staged protests inside their respective companies against launching joint ventures with the federal government that would "weaponize" cloud-based video recognition software. Both companies offer cloud-based video recognition services, where anyone with a credit card can sign up for a service that analyzes real-time video to identify objects and people. In both cases this offended the employees, who demanded that the companies not work with the federal government on deploying these technologies to be used in war (such as analyzing drone footage from war zones) or security services (such as identifying people who've been caught crossing the border under suspicious circumstances).
China has none of those concerns, and is instead proceeding with full speed (according to the NY Times) on developing facial recognition technology, and deploying it among security forces.
Scenarios:
- In Zhengzhou, a police officer wearing facial recognition glasses caught a heroin smuggler
- In Qingdao, cameras watching the crowd at a big annual beer festival helped police capture two dozen criminal suspects
- In Wuhu, a fugitive murder suspect was identified by a street camera while buying food at a street vendor cart
Among those scenarios is a pair of new technological objects. One, "facial recognition glasses", look like sunglasses but contain cameras and a connection to cloud-based computing systems. Captured images are scanned for faces, and faces are matched against a database of criminal suspects, and any match then alerts the officer wearing the glasses.
The other is a camera watching a crowd, or watching a street. Police forces around the world, even in the USA, have been deploying cameras for remote monitoring of intersections and sidewalks. What's new is to feed the video through a software system, for example to count the number of unique people in a crowd, or to identify everyone in a crowd.
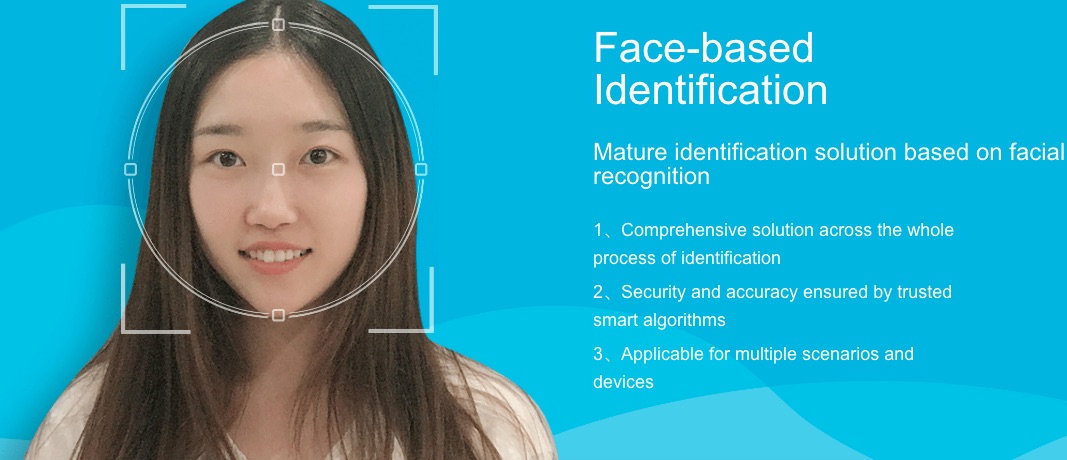
The Chinese government is working with several companies on the goal of implementing a ubiquitous monitoring system. One of those is Megvii, whose
Face++ website goes over the technological offerings. Scroll down to the bottom of the page, and you'll find a link to a Chinese version of the website.
The technology areas offered by Megvii includes:
- Facial Recognition
- Face Detection: Face++ detects and locates human faces within an image, and returns high-precision face bounding boxes.
- Face Comparing: Check the likelihood that two faces belong to the same person.
- Face Searching: Find similar-looking faces to a new face, from a given collection of faces.
- Face Landmarks: Locate and return keypoints of face components, including face contour, eye, eyebrow, lip and nose contour.
- Face Attributes: Face++ analyzes a series of face related attributes based on machine learning technologies. You can get face attributes including age, gender, smile intensity, head pose, eye status, emotion, beauty, eye gaze, mouth status, skin status, ethnicity, face image quality and blurriness.
- Emotion Recognition: Analyze and identify emotion of detected faces. Analysis result of each detected face includes confidence scores for seven kinds of emotion : anger, disgust, fear, happiness, neutral, sadness, and surprise.
- Beauty Score: Compute beauty scores for detected faces from both male's and female's perspective.
- Gaze Estimation: Face++ can estimate eye gaze direction in images, compute and return high-precision eye center positions and eye gaze direction vectors.
- Skin-status Evaluation: Evaluate skin health status of detected faces, and recognize common skin problems, such as acne, dark circles, and spots on face.
- Body Recognition
- Body Detection: Face++ detects and locates human bodies within an image, and returns high-precision body bounding boxes.
- Body Outlining: Detect outlines of bodies within one image, and return a string consisting of floating-point numbers.
- Body Attributes: Face++ analyzes a series of body related attributes based on machine learning technologies.
- Gesture Recognition: Detect and return locations of all the hands within images, and recognize hand gestures.
- Image Recognition
- Face Merging: Merge faces in the template image and the merging image and return the merged image.
To take an example - Face Searching is a service supporting Find similar-looking faces to a new face, from a given collection of faces. Suppose someone comes to the front door of an office building, how does security know if that person legitimately belongs in that building? Maybe illegitimately they're claiming to have lost their ID badge, and are requesting entry? With Face Searching the company can keep a database of facial images of their employees, and this person in the lobby can be checked against that database.
Or, a government could have a series of cameras throughout a city. The video streams are sent through Face Detection software to extract the faces from the video, then using Face Searching or Face Comparing techniques any miscreants can be identified from a database of subjects. Or maybe Emotion Recognition can be used to identify the nervous people, because it's well known that miscreants on a dangerous mission will seem nervous. Or maybe a Body Outlining algorithm can be used to detect people with backpacks, because a bomb might be in a backpack.
A use case described for Face Detection is to count the people in a crowd using faces. Clearly it's difficult to count the number of people in a crowd, but if you had automated software that detected every face in the crowd, then compared faces against each other, you would have a list of unique faces. If your system was ubiquitous enough to capture every face in the crowd, then the system can reliably count the number of people in the crowd.
But of course such a system can be used to .... track where everyone goes, and who everyone talks to. For example, China's government has set up systems in West China to track members of the Uighur Muslim minority and map their relations with friends and family. The Uighur minority in China is already oppressed, and obviously the Government does not want to risk anything from members of that community.
Another use is to shame folks who jaywalk. With images captured through cameras, the government can identify folks who illegally cross the street (a.k.a. jaywalking). Pictures of these people, along with their name and government ID number, are displayed on billboards around the city in an effort to shame people into obedience.
Clearly there are benign uses of facial recognition technology. For example the Face Merge feature offered by Megvii can be a fun thing - take two "Selfies" of two friends, and they can have fun seeing what their merged faces look like. Or a social media network can use this to auto-tag folks who are in pictures.
But just as clearly this can be deployed as the means for autocratic control of the population. When the government knows everyone's location, knows who they've talked to, and even has an automated emotion recognition system, the result is not likely to be pretty.