; Date: Fri Mar 30 2018
Tags: Facebook »»»» Privacy »»»»
A meme going around says -- "I spoke aloud yesterday about cialis, and now my Facebook feed is full of ads about Cialis". The reality isn't quite that bad, but yesterday I opened the TransferWise website for one page view, and now Facebook is showing me a TransferWise advertisement. How did Facebook know I visited that website? how did TransferWise know to put advertising in front of me? Isn't this a privacy violation?
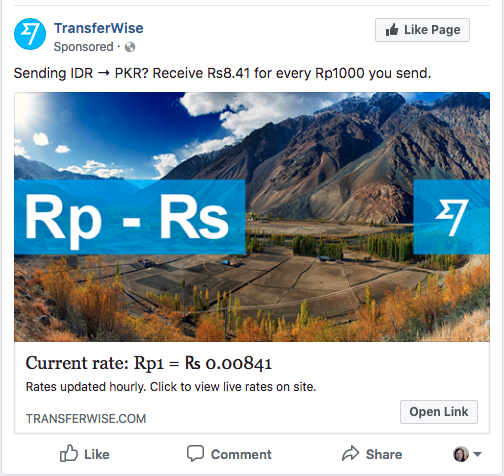
Situation: I've heard of TransferWise as a less expensive way to exchange currencies. They've developed an ingenious way around the normal money exchanger networks, and can therefore charge a lower money-changing fee. Jesus may have kicked the moneychangers out of the temple because they charged him a high fee?
Anyway, I've had one tab open in my browser on the TransferWise website for a couple months meaning to read more. Yes, I'm one of those who "hoard tabs". Yesterday I had to restart my browser, which meant all the tabs (including the TransferWise tab) saw one new page view. I did nothing further with the TransferWise website than that.
Today? I'm scrolling down the Facebook news feed and see the advertisement shown above.
Everybody has had this experience. They'll type a search phrase in the search engine, and for the next week they'll be inundated with advertising on that search phrase. Or they make an Amazon search, and suddenly they're getting advertising for that thing. Even on services completely disconnected from that search engine or from Amazon or whatever.
Lots of folks are asking why banner ads follow them from site to site. This can be eerie, somehow the ad companies know your actions and showing you the same advertisement. Are we all being followed around by Google or Facebook or others?
Isn't it a privacy violation? How did the knowledge of action A on one site become advertising following you around the web? How did that get communicated? And isn't there a nefarious use for this? It's one thing that we're inundated with advertising based on websites we've visited, but what if Big Brother is tapping into this information stream?
Retargeting
The key technology is called Retargeting or Remarketing. This is a "form of online advertising that can help you keep your brand in front of bounced traffic after they leave your website."
To degobbledygook that -- Remarketing enables an advertiser to put advertising in front of people who've visited the corresponding website.
Behavioral retargeting[Wikipedia] (also known as behavioral remarketing, or simply, retargeting) is a form of online targeted advertising by which online advertising is targeted to consumers based on their previous Internet actions. Retargeting tags online users by including a pixel within the target webpage or email, which sets a cookie in the user's browser. Once the cookie is set, the advertiser is able to show display ads to that user elsewhere on the internet via an ad exchange.
The implementation uses a 1x1 invisible image (a.k.a. "pixel") that's included in the web page. That 1x1 image comes along with a cookie, and the cookie is refreshed every time the user visits the website. The image is supplied by a service provider, a.k.a. remarketing provider, who is collecting information about website visitors. That information is then used to drive advertising programs.
The idea is - target the advertising on folks who already know about the "brand". If one exposure to a "brand" was not enough, then repeated exposure is sure to cause a sale. In theory. Me? It gives me creepy heeby jeebies.
The information collected is not personal identifying data. All that can be collected this way is an anonymous identifier for the browser. For example the inserted cookie might contain a randomized anonymous string like 7c649fcc-2b46-4270-93b6-d65ba6f1388f. The remarketing provider uses that anonymous identifier to track visitors to the website.
It may be that the remarketing provider has pixels installed on multiple websites. If so, the remarketing provider can begin to collect a profile when the same web browser visits multiple websites. Say a person is comparison shopping for digital cameras and therefore visiting multiple camera manufacturer and camera review websites. The remarketing provider can see this in the profile. An advertiser, say a camera store, can then target their advertising spend on folks who've shown an interest in digital cameras.
Retargeting versus Remarketing
What's the difference between Retargeting and Remarketing? They're not quite the same phrase.
Retargeting focuses on delivering advertising to folks who've previously visited a website. Suppose you visited not just a website, but a particular page on a website, the retargeting can then inundate you with advertising for the product on the page you visited.
Remarketing focuses on "re-engaging" users with e-mail. For example, you might recieve an email because you put a product in a shopping cart then did not follow through with a purchase.
Privacy concerns
Wikipedia has this to say:
In the United States, several organizations, including the Federal Trade Commission, Congress and the media, have expressed privacy[NYTIMES] concerns around the practice of retargeting; however, responsible personalized retargeting providers don’t collect personally identifiable information (PII) on consumers. Providers are blind to a user’s age, sex and other personal information. Instead, providers rely upon data gathered from cookies that are placed on a consumer’s browser by the websites they visit. This information is not shared among publishers, other advertisers or third parties and cannot be linked to a specific user. The United States hasn’t legislated many laws around the practice, and instead relies upon the industry and its overarching organizations, such as the Interactive Advertising Bureau, Network Advertising Initiative and TRUSTe to self-regulate. In October 2010, the IAB announced its Advertising Option Icon, which partner sites will place near banner advertisements that collect non-PII user data.
This statement sounds nice - that remarketing providers are acting legitimately and with integrity. Is it reality?
The technique can connect together actions by users on multiple sites. While it doesn't directly get age/sex/etc with enough data-points one can build up an information profile of folks. With enough data it might be possible to identify specific people.
Consider that part of the received information will be the users IP address. How? When the pixel is retrieved, the software receives the IP address of the browser requesting the pixel. It has to know the IP address because an Internet socket has that data available.